The Fugue Best Practices Framework is designed to complement standards such as the CIS Foundations Benchmark to provide the most comprehensive protection against today's advanced misconfiguration attacks.
Cloud misconfiguration is the number one cause of data breaches involving public cloud services such as those offered by AWS.
While compliance frameworks such as the CIS Foundations Benchmarks address a number of cloud misconfiguration risks, recent major cloud-based data breaches were possible due to misconfigurations not necessarily covered by these standards. [Read A Technical Analysis of the Capital One Cloud Misconfiguration Breach]
The Fugue Best Practices Framework includes rules covering the following cloud vulnerabilities:
- Identity and Access Management (IAM) misconfigurations that can provide bad actors, including malicious insiders with the ability to move laterally and discover resources to exploit
- Object storage policy misconfigurations that can be exploited in order to take data exfiltration actions
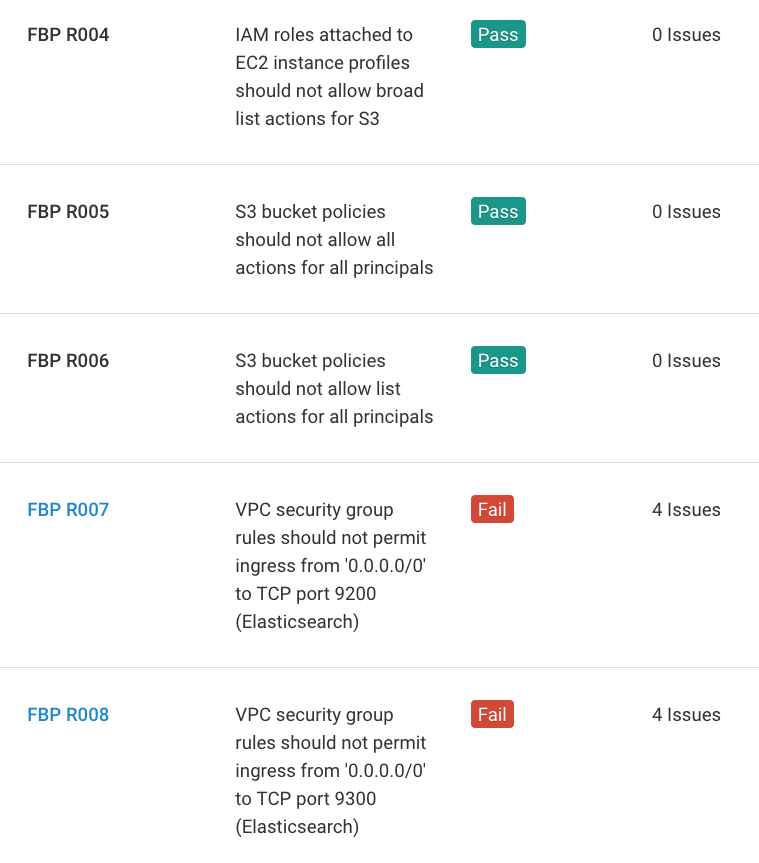
- Network security group rule misconfigurations that can enable malicious access via Elasticsearch, etc, MongoDB, and other services
Fugue will continue to add new rules to the Fugue Best Practices Framework as new misconfiguration vulnerabilities and attack vectors are identified.
Identify Advanced Cloud Misconfiguration Risks
Within minutes, Fugue identifies critical cloud resource misconfigurations in your cloud environment that violate the Fugue Best Practices Framework. Fugue then continuously evaluates your environment to alert you on any changes that create new misconfiguration risks. Fugue provides cloud teams with detailed information on each misconfiguration in order to correct them.
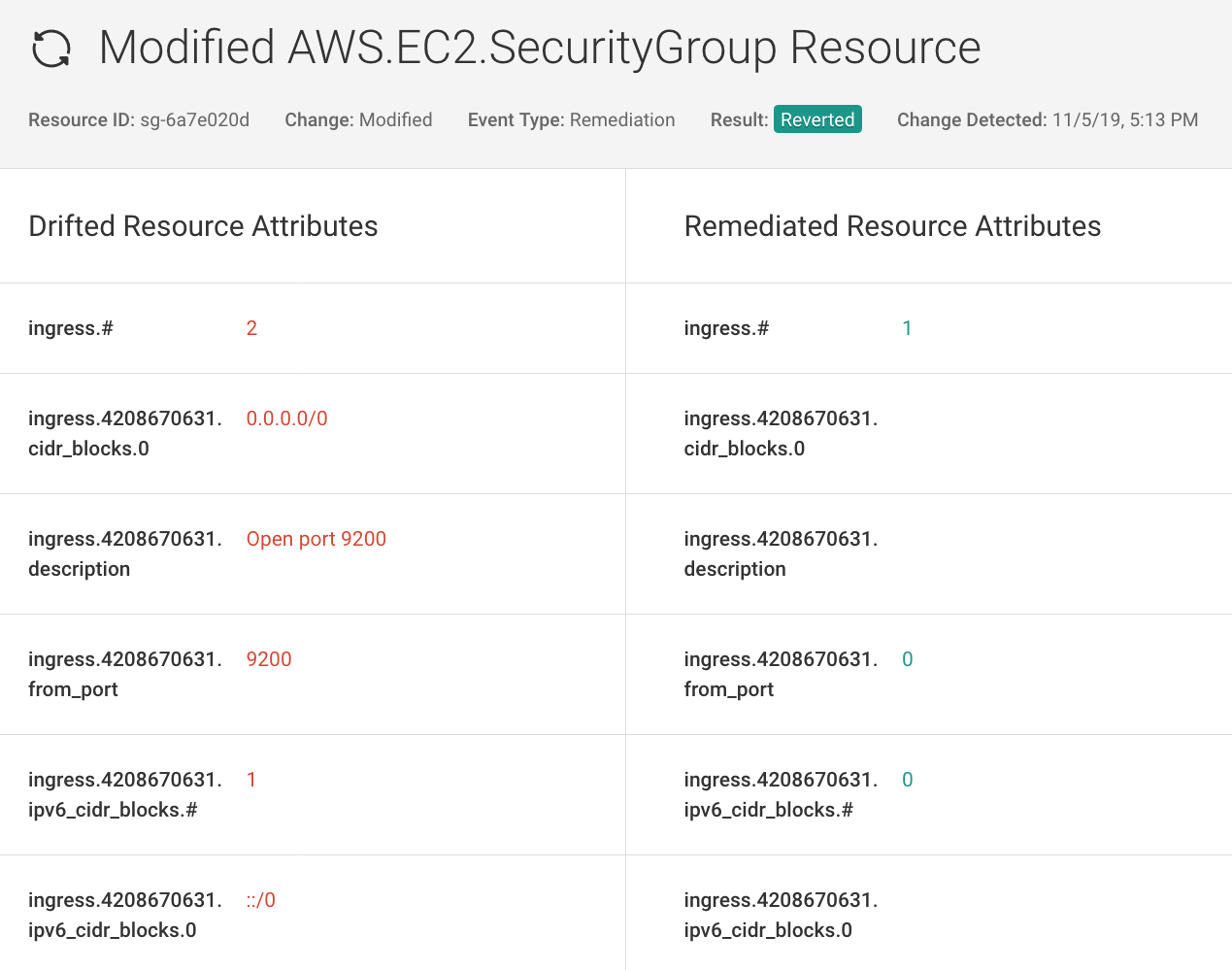
Enforce Baselines with Codeless Auto-Remediation
Baseline your cloud environment with Fugue to monitor for changes that create new resources misconfiguration vulnerabilities. For security-critical resources, employ baseline enforcement to correct any authorized change back to your established baseline without writing and managing automation scripts or bots.
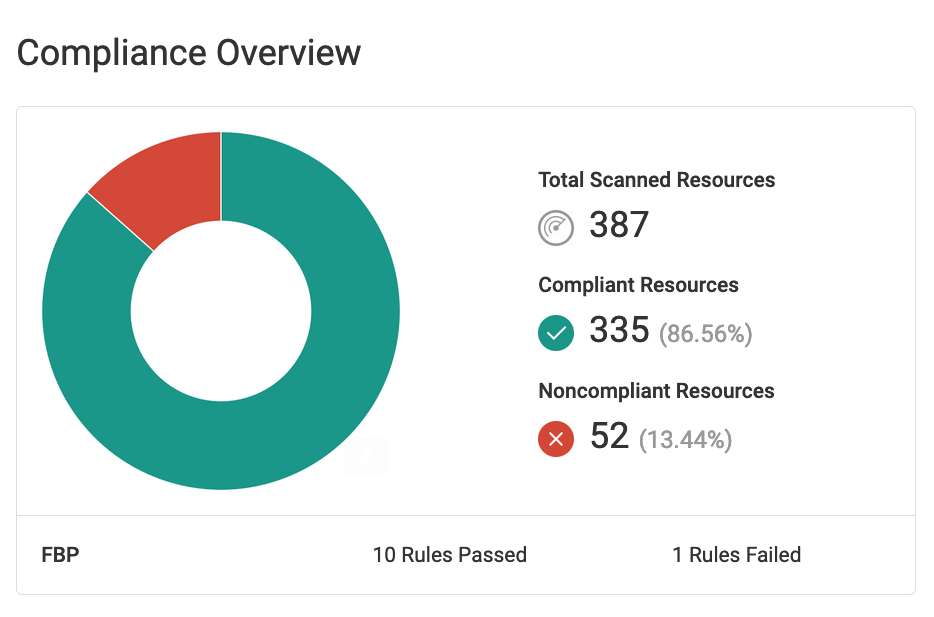
Report on Your Cloud Security Posture
Fugue makes it easy to report on your cloud posture for the Fugue Best Practices Framework, standards like CIS Foundations Benchmarks, GDPR, HIPAA, ISO 27001, NIST 800-53, PCI and SOC 2, and your own custom enterprise security policies.
Detailed reports, dashboards, and visualizations are available to easily track and monitor your cloud resources. Daily or weekly reports highlighting compliant and non-compliant resources can be emailed to executives or auditors to show proof of compliance.