ISO 27001 focuses on establishing, implementing, maintaining, and improving an information security management system (ISMS). It is the best-known compliance standard within the ISO/IEC 27000 family of standards, which covers the overall safety of information assets. By maintaining compliance with ISO 27001 controls, an organization of any size in any business sector can help protect digital information such as intellectual property, financial information, employee details, and more.
ISO 27001 Compliance
ISO 27001 is divided into two different sets of clauses that promote information asset security:
- Clauses 1-10 broadly focus
on creation and implementation of an information security management system. - Annex A contains 114 controls specifically concerning
application of a risk management process.
To be ISO 27001 compliant, an organization should address clauses 1-10 in addition to applicable Annex A controls. These controls are determined through Clause 6.1.2, which requires an organization to perform a risk assessment, and Clause 6.1.3, which mandates applying the necessary Annex A controls to treat the identified risks.
For example, Annex control A.17.1.2 concerns "Implementing information security continuity," which organizations using AWS RDS can address by requiring RDS instances to have multiple subnets. Organizations using Google Cloud can ensure SQL database instance automated backups are enabled.
While it's important to review all ISO 27001 clauses and controls for overall compliance, the following Annex A controls are the most relevant for organizations in the cloud.
A.6 Organization of information security
A.8 Asset management
A.9 Access control
A.10
A12 Operations security
A.13 Communications security
A.14 System acquisition, development, and maintenance
A.17 Information security aspects of business continuity management
Detect Compliance Violations
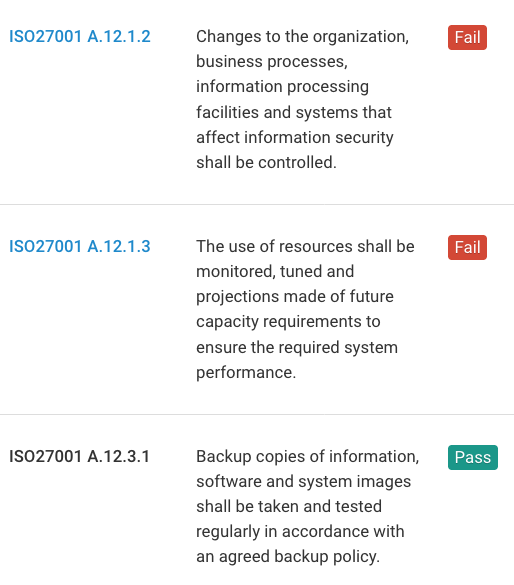
Fugue continuously evaluates your cloud environments for ISO 27001 compliance violations with predefined rules mapped to ISO 27001 compliance controls. If a resource is determined as non-compliant, an alert will be sent to notify the compliance team. The compliance team can then determine whether to correct the non-compliant resource and set an established baseline for future enforcement.
Detect Compliance Violations
Enforce Baselines with Codeless Auto-Remediation
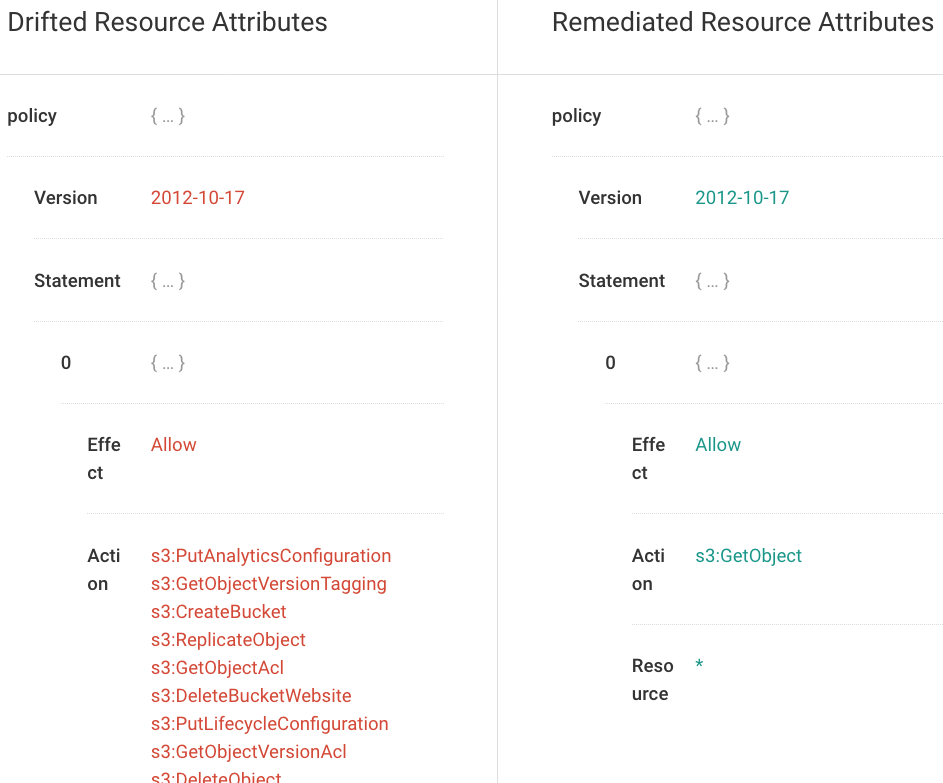
Fugue utilizes baselines to auto-remediate and correct compliance violations via self-healing. A baseline is a known-good configuration state for resources agreed upon by stakeholders. With baseline enforcement, misconfiguration is automatically corrected back to the ISO 27001-compliant baseline without writing automation scripts.
Enforce Baselines with Codeless Auto-Remediation
Report on Compliance Posture
Fugue makes it easy to report on your ISO 27001 compliance posture. Detailed reports, dashboards, and visualizations are available to easily track and monitor your cloud resources. Daily or weekly reports highlighting compliant and non-compliant resources can be emailed to executives or auditors to show proof of compliance.
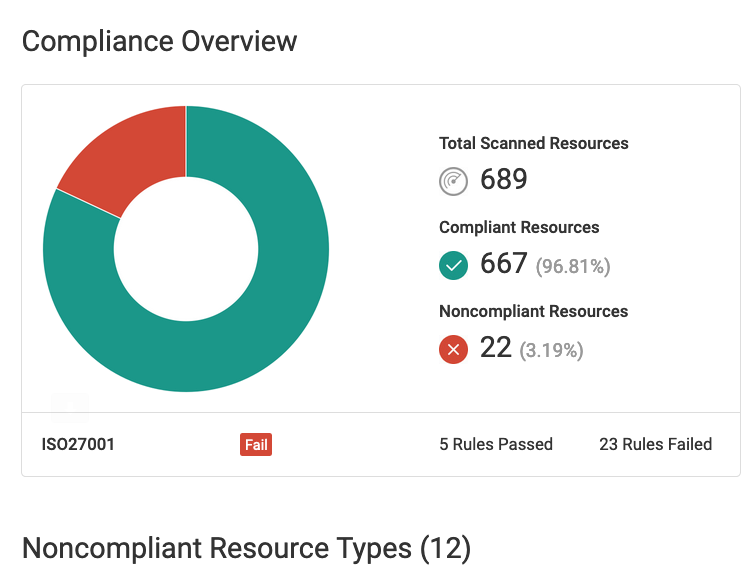
Compliance Overview
