One Set of Policies Governs All Cloud Operations
All cloud stakeholders (developers, operations, security, and compliance) operate efficiently under a single source of truth for cloud policy.
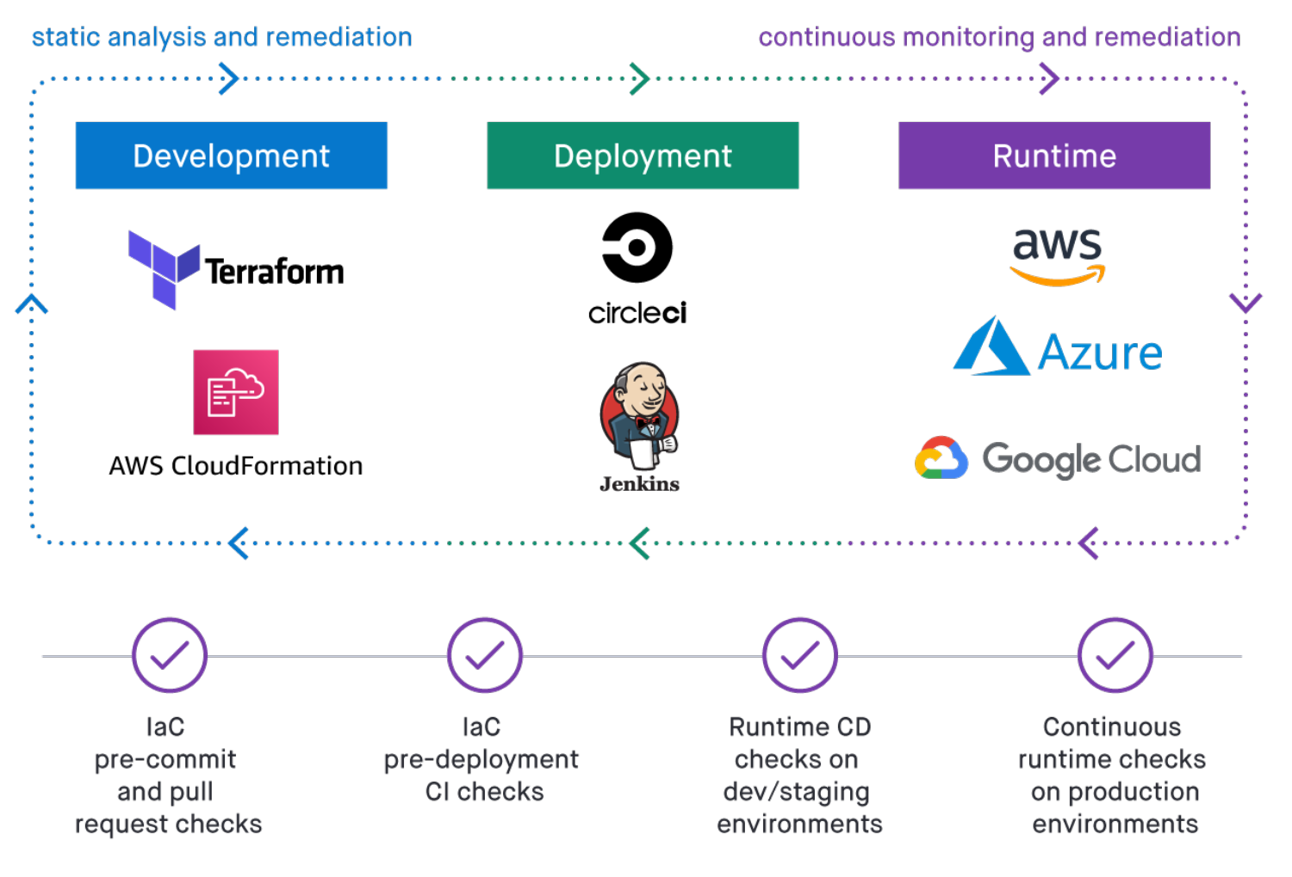
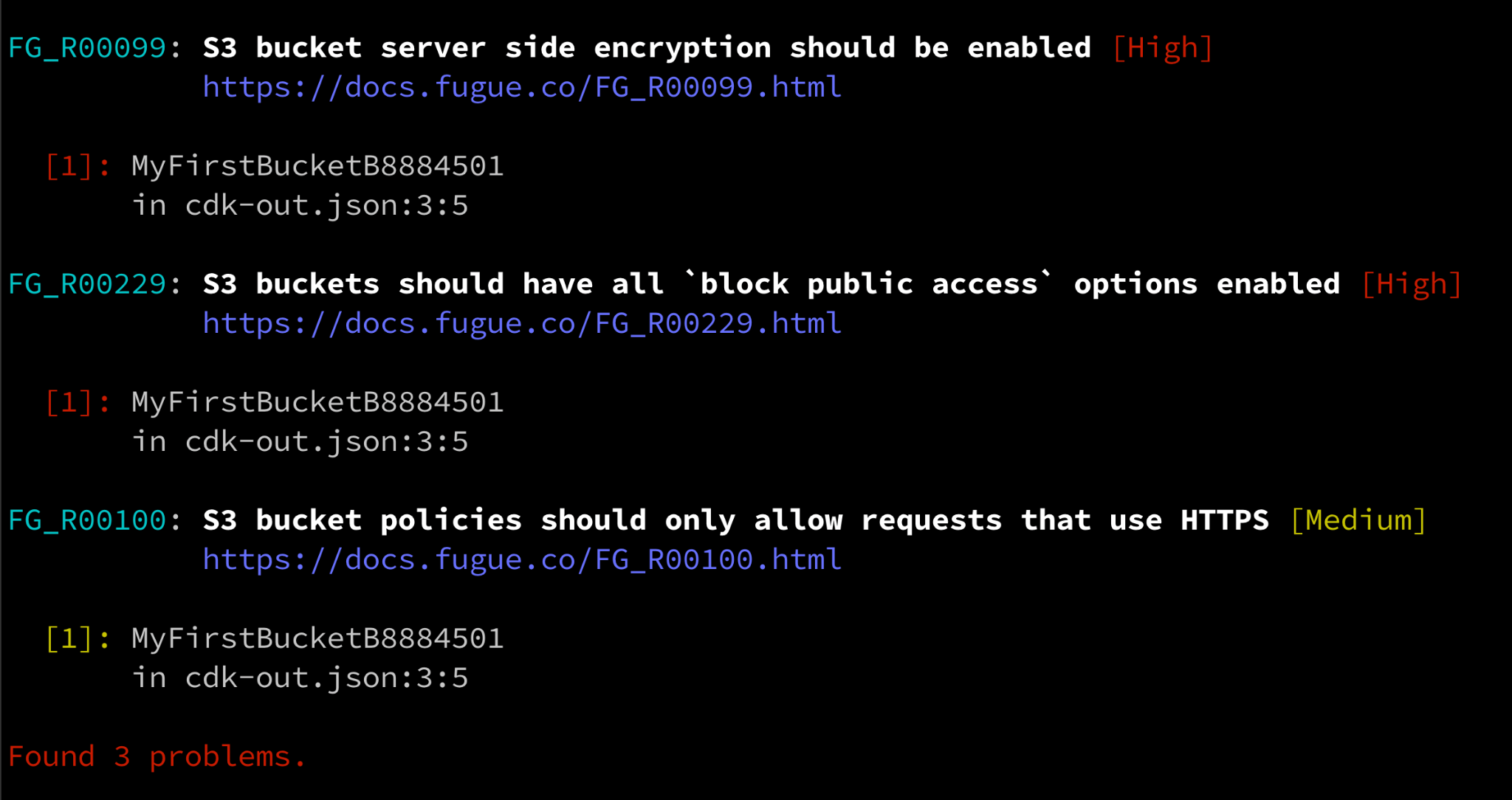
- Deliver secure IaC fast. A single misconfiguration in IaC can become a critical runtime vulnerability. Find and remediate security issues quickly when developing IaC and move forward.
- Prevent misconfiguration in CI/CD. Security checks on individual IaC modules aren’t enough. Catch misconfiguration in deployment pipelines and avoid runtime vulnerabilities.
- Keep your cloud runtime secure. What’s secure on day one can drift on day two. Keep your cloud free of misconfiguration and in compliance—regardless of how you deploy it.
Policy as Code Automation for Multi-cloud
For cloud security to be efficient and effective, it must work with the tools, workflows, and requirements you have today—and tomorrow.
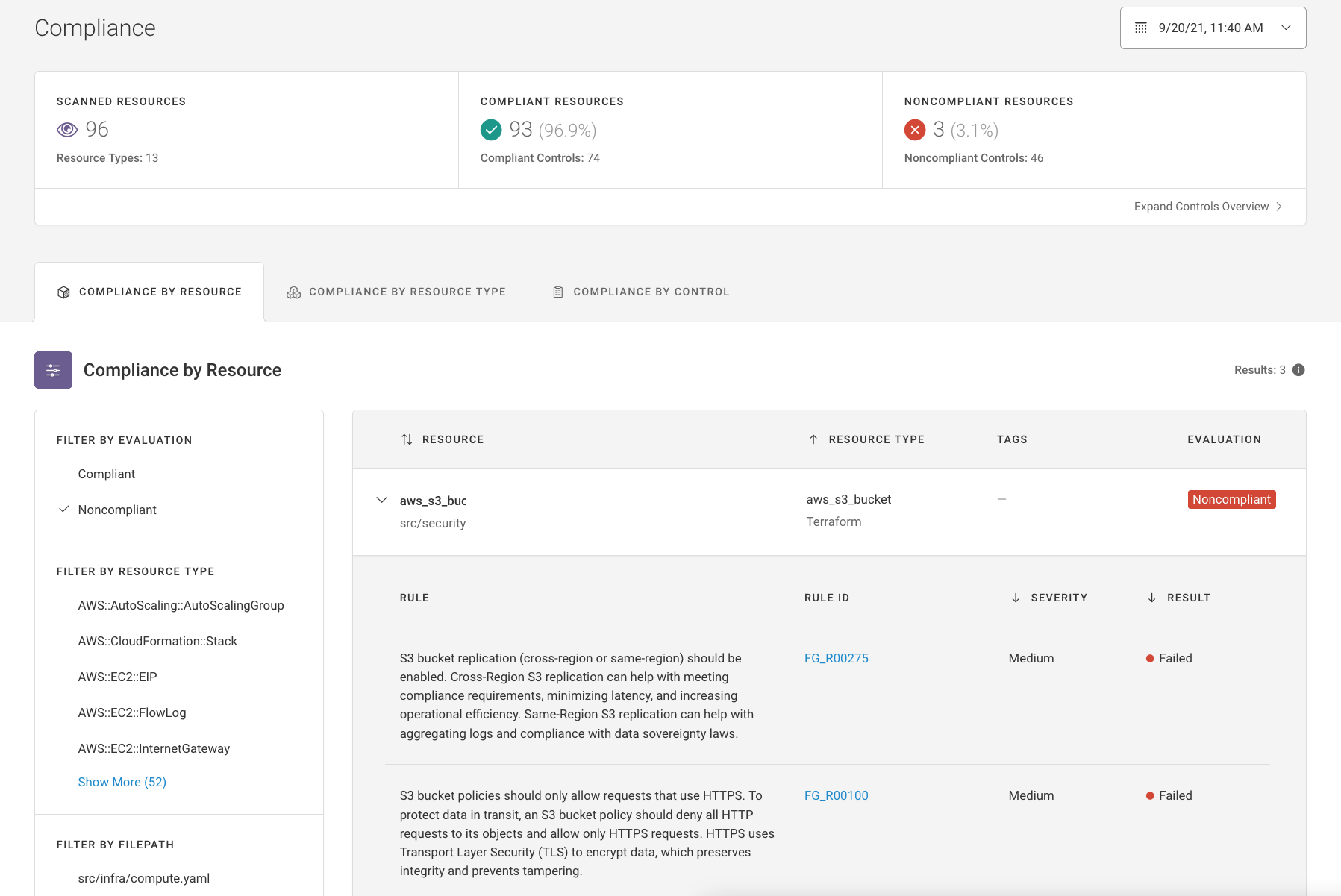
- Consistent governance across cloud platforms. Using multiple cloud providers shouldn’t be a security burden. Apply policy consistently across AWS, Azure, and Google Cloud.
- Integrate cloud security Into DevOps. Run IaC policy checks on Terraform, AWS CloudFormation, and Kubernetes manifests and automate guardrails in your CI/CD toolchain.
- Leverage turnkey cloud compliance. Deploy hundreds of pre-built policies mapped to the common industry compliance families, such as SOC 2, NIST 800-53, and PCI.
Cloud Security Powered by Open Policy Agent
Establish your cloud security foundation on Open Policy Agent (OPA)—the open source standard for policy as code.
- Catch vulnerabilities involving multiple resources. With Fugue, eliminate dangerous misconfigurations that single-resource policy checks can't detect.
- Develop policy as code using an open-source language. Use Rego, OPA’s language that is easy-to-learn and flexible enough to address the most complex enterprise use cases.
- Use developer-friendly tools for testing policies. Leverage open source OPA-based tools such as Regula to develop, test and run security checks on IaC locally.
Unified Policy Engine and Resource Data Engine
Together with Fugue’s Resource Data Engine—which continuously captures the complete configuration state of your running cloud environment—Fugue’s Unified Policy Engine empowers teams to apply policy as code automation everywhere they’re operating in the cloud.
Learn what Fugue’s Unified Policy Engine and Resource Data Engine makes possible:
