On January 1, 2020, the California Consumer Privacy Act (CCPA), California’s answer to GDPR, goes into effect. Like GDPR, the CCPA is delivering anxiety and dread to executives, marketers, compliance officers, and engineers everywhere. As we learned from numerous conversations at the AWS re:Invent 2019 conference last week, engineers responsible for building and managing cloud-based systems and data are focused on CCPA and what it means.
But what CCPA mandates for cloud infrastructure is vague, and it’s this vagueness that dominated these conversations. “Hand-wavy” was the common refrain. Sure, the CCPA doesn’t look anything like, say, NIST 800-53, with its thousands of detailed, prescriptive controls. And thank goodness for that! The lack of specificity affords us the flexibility to bring disparate IT systems and processes into compliance.
This post focuses on how CCPA impacts cloud infrastructure operations and those who build and manage cloud-based systems (e.g., DevOps; cloud engineers; cloud architects; security engineers). But it has relevance for anyone who makes decisions about compute infrastructure and data as well.
What is the CCPA?
There’s plenty of detailed information out there about the CCPA, so I’m not going to belabor details here. It’s sort of like the GDPR, but different. Like the GDPR, the CCPA entitles individuals to know what personal information has--and is--being collected from them and with whom their data is shared. Individuals have the right to access their information and have it erased upon request. It also requires information holders to keep data secure and private.
There are indications that such requests will be common, if not widespread. This will be thornier for adtech companies that are built on this kind of information, and since many companies have marketing operations that leverage adtech services, they’ll need to ensure the adtech services they use comply with the CCPA, and can facilitate CCPA requests.
If you’ve already established compliance with GDPR, you’re likely ahead of the CCPA game.
The CCPA gives individuals rights to their data
California individuals will now have the right to 1) know what information you have collected on them, 2) have access to that information, 3) object to the sale of their information, and 4) request the erasure of their information from your systems. Companies face significant financial penalties for failing to comply with such requests. The CCPA definition of personally identifiable information (PII) is quite broad, including the obvious (names, SSNs, etc) as well as biometric information, search and browser histories, and “probabilistic identifiers.”
For cloud ops, this means you must establish and maintain authorized discoverability, visibility, and access into your cloud infrastructure environment and closely track which resources contain what sensitive data. This must encompass database and object storage services as well as backups and snapshots.
The CCPA compels the privacy and security of data
Under the CCPA, the California Attorney General can sue companies for breach of privacy if personally identifiable information data is mishandled or breached. This can (and likely will) include data exposures and leaks that didn’t result in an actual breach.
For cloud ops and security, this means you must deny unauthorized discoverability, visibility, and access to your cloud infrastructure environment and data. Cloud resources must be securely configured and encrypted, and this configuration state must be continuously monitored and enforced to prevent misconfiguration--the number one cause of cloud-based breaches. Be sure to include all data backups and snapshots in your cloud security posture management, and collect all audit and log data for cloud resource access and data transactions.
Because the cloud is 100% programmable, embrace infrastructure as code (e.g., Terraform; AWS CloudFormation) and policy-as-code (e.g. Open Policy Agent; Rego policy language) to ensure compliance at scale and the ability to prove compliance at any time. You’ll also save time and money and greatly reduce the risk of human error.
Bring your cloud environment into compliance with GDPR, and apply an additional standard like the CIS Foundations Benchmarks for Amazon Web Services (AWS) and Microsoft Azure. This will help you keep your infrastructure and data secure and demonstrate your commitment. Policy-as-code libraries exist that you can leverage in this effort.
AWS has produced a white paper regarding their cloud services and CCPA here. Microsoft provides CCPA information here.
Comply with CCPA, even if it doesn’t apply to you
Unlike GDPR, The CCPA only applies to companies that:
- Have annual revenues of $25MM or more
- Collect, share, buy, or sell data of more than 50,000 Californians
- Derive 50% or more of revenue by the sale of California consumer data
Unless you’re operating a small business and plan to keep it that way, these exemptions may only buy you a little time. The CCPA regulations are likely to change, and those changes may be substantial. Other states are considering their own versions of CCPA, and while Congress may be in a state of gridlock now, that won’t last forever. Anticipate federal consumer data privacy and security regulations within the next few years.
Many companies chose to simply not serve EU citizens rather than comply with GDPR. It’s not likely that those companies can afford to let go of California, and possibly the remaining United States for that matter in due time. When you see “California resident” in the CCPA regulations, consider it “U.S. resident.”
Your CCPA options: endure some pain now or much pain later
Security and compliance is a game of yardage. You want to push as far down the field as early as you can. Keep going, and eventually you’ll put points on the board. You’re not going to score a breakaway touchdown, but you can lose quickly if you fail to move the ball.
Bringing your systems and procedures into compliance earlier on--even if you’re not currently required by law to do so--will pay dividends down the line. You’ll earn the trust of your customers, help avoid data breaches and compliance fines, and help avoid increasingly costly compliance efforts later as more regulations are surely to come.
Like with GDPR, there will be high profile examples of compliance failure and hefty penalties. Don’t become the example with CCPA. It is extraordinarily difficult to retrofit systems to new architectural requirements, so bake them in as soon as you can.
One more thing…
Fugue is cloud security and compliance. Built for engineers, by engineers. With Fugue, you can:
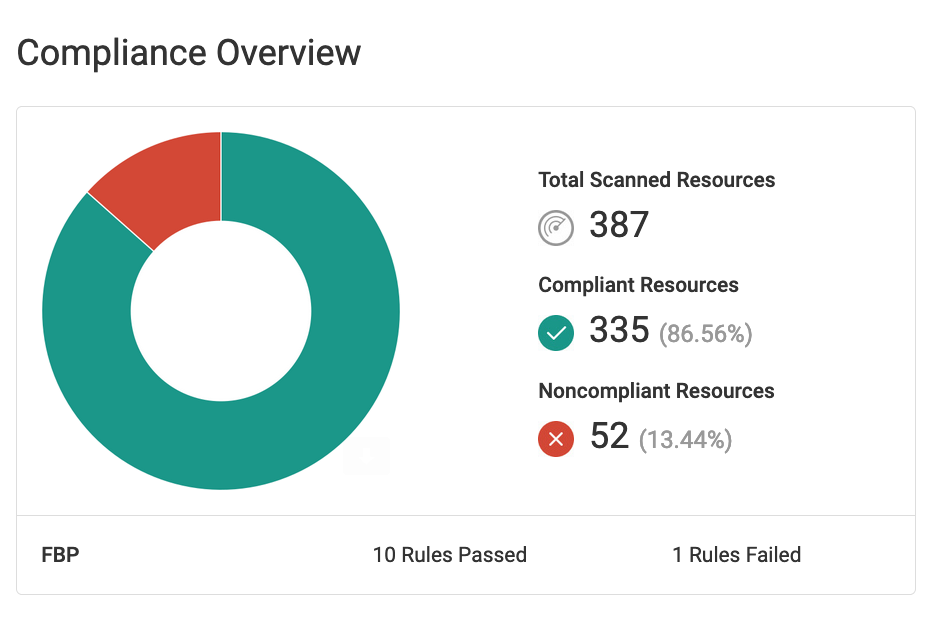
- Get complete visibility into your cloud infrastructure environment and security posture with dynamic visualizations and compliance reporting.
- Validate compliance at every stage of your software development life cycle for CIS Foundations Benchmark, HIPAA, PCI, SOC 2, NIST 800-53, ISO 27001, GDPR, and your custom policies.
- Protect against cloud misconfiguration with baseline enforcement to make security critical cloud infrastructure self-healing.
Fugue Developer is free forever for individual engineers. Get started here.